Note from Kevin: Parts of this article were first published on Runway Girl Network at http://www.runwaygirlnetwork.com/2015/01/13/gogo-no-longer-issuing-fake-google-ssl-certificates/. I encourage you to visit Runway Girl Network for unique analysis in the Passenger Experience field.
For those of you who use Gogo in the air will notice that YouTube is accessible again (as I tested on Friday), and retested on Tuesday aboard US425 Phoenix to New York JFK
YouTube working through Mozilla FireFox; it was taken at 11:01 Phoenix time on 13 January on board US Airways flight US425 between Phoenix and New York JFK.
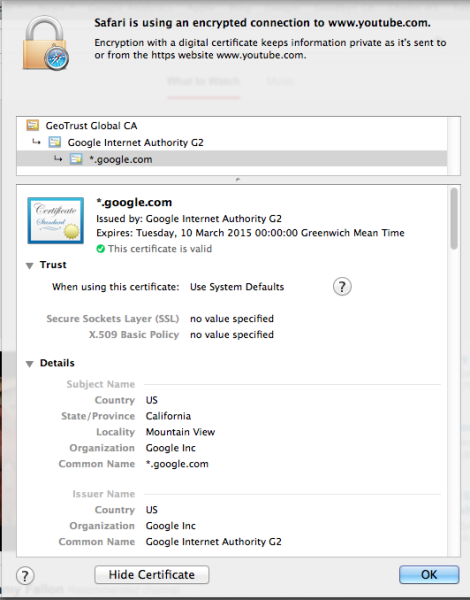
A correct certificate is also showing in Apple Safari too:
Extract of the valid certificate via Apple Safari, taken 10:52 Phoenix Time, Tuesday 13th January, US Airways Flight US425 Phoenix to New York JFK.
Runway Girl Network has spoken to Gogo’s Steven Nolan, stating:
“Yes, I can confirm we are no longer using that technique”
Lets take a step back.
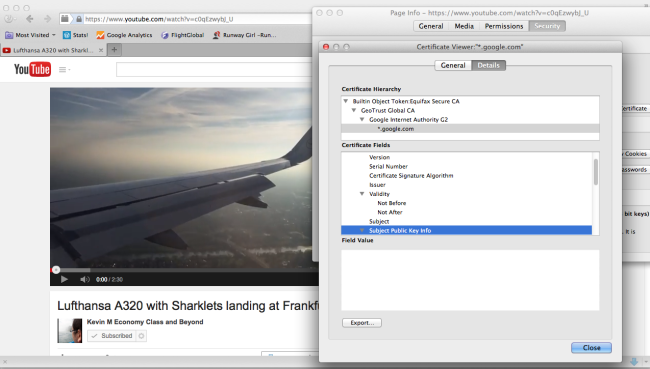
Last week Gogo were spotted replacing YouTube/Google Certificates with their own:
The “fake” Google one looks like this – as reported by Adrienne Porter Felt:
hey @Gogo, why are you issuing *.google.com certificates on your planes? pic.twitter.com/UmpIQ2pDaU
— Adrienne Porter Felt (@__apf__) January 2, 2015
Gogo responded with a statement:
What did Gogo do that was such a bad thing?
The Internet is built on many things – servers, cables, satellites – but a core element of this is something far more fundamental than the technology – TRUST.
Digital Certificates (or Public Key Certificates) are used in trusted environment to ensure a transmission from a computer to a user and back again is a “trusted” and “encrypted” link – ensuring only those parties can communicate.
You’ll see these every day – be it shopping on Amazon, banking with your online banking provider, shopping online with your supermarket, shopping for flights with your favourite airline or online travel agent.
And most of us don’t pay attention – all we look for a is a padlock and a green bit of text.
However, we must look beyond this.
With Gogo introducing its own certificate (which is akin to an “attack” of sorts – called a Man in the Middle Attack), a third-party can potentially decrypted what you’ve been up to, or if you’ve been trying to watch Youtube on a plane – what you’ve been watching. Introducing the MitM vector allows Gogo to create a “white-list” of sorts, controlling what content you see.
And that’s dangerous from a personal security perspective, but also from a situation of trying to “crack a nut with a hammer”.
There are many technical ways that achieve the same thing – be it IP Blocking, Name Looking, Access Control Lists – it goes on. All easier to implement from a technical viewpoint.
So why Fake Certificates?
YouTube by default operates in an encrypted transmission mode. Thus blocking streams from YouTube is a very tough thing to do without blocking the entire site. Therefore using MitM style attacks can preserve precious bandwidth in the sky and share it appropriately between all the subscribers on the plane.
Of course, it goes without saying you shouldn’t be streaming in the sky as it’s against Gogo’s Terms and Conditions.
Gogo denied snooping on any passengers, stating:
“no user information is being collected when any of these techniques are being used. They are simply ways of making sure all passengers who want to access the Internet in-flight have a good experience.”
Gogo’s record has been less than spotless in that respect.
What you can do:
Don’t rely on the padlock, or the green bar. If you get an error about a certificate when you browse a page, Look at it, examine it and question it
There is plenty of scaremongering in the IT Industry, and the actions of Gogo didn’t inspire confidence. Now they’ve rolled back the change, it’s a bit better.
But as usual – be careful when you’re browsing the web, using Internet services that you’re not familiar with. If it looks too good to be true… it probably is.
Welcome to Economy Class and Beyond – Your no-nonsense guide to network news, honest reviews, with in-depth coverage, unique research as well as the humour and madness as I only know how to deliver.
Follow me on Twitter at @EconomyBeyond for the latest updates!
Also remember that as well as being part of BoardingArea, we’re also part of BoardingArea.eu, delivering frequent flyer news, miles and points to European readers